SPART

The SPART jammer, a champion in the electronic warfare world
Remotely neutralize radio-controlled improvised explosive devices (RCIEDs) and drones in real time. No threat using radio frequency (RF) signals is immune to SPART.
SPART offers advanced protection against RCIEDs and other RF threats with simple operational use thanks to full digital pre-mission programming. Take it anywhere, SPART can be used in a variety of configurations and environments. Compliant with safety standards, it is safe for operators.
SPART is the best ally for forces in the field. It neutralizes RF signals, jamming telecommunications and geo-positioning systems. What’s more, it is capable of luring by replay.


Origin
Solution designed according to the specifications of Commandos Kieffer and the DGA.

Deployment
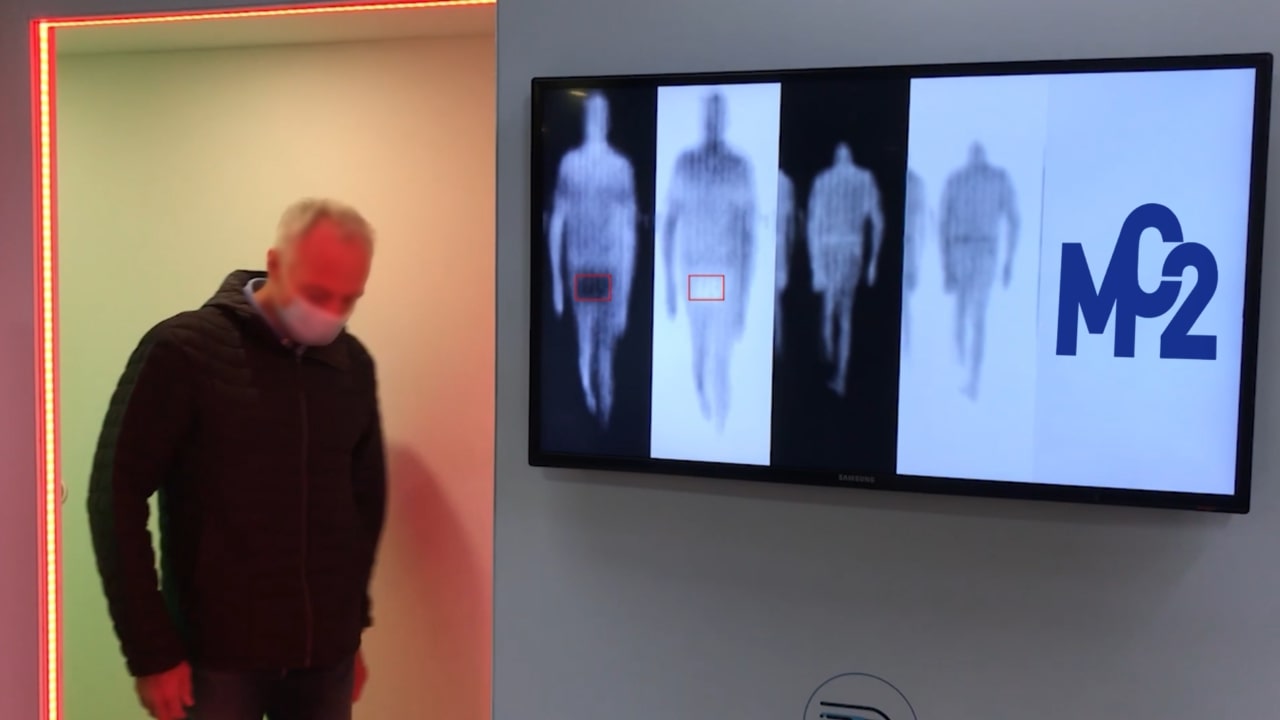
Securing public places for the Paris 2024 Olympic Games.

Customers
French Special Forces
French Ministry of the Interior
SPART, the infantryman’s essential
Tested and deployed by forces in France and abroad, SPART enables troops to advance against the threat of drones and RCIEDs.
Fully programmable, the jamming system is 100% customizable before deployment.
Like our mission preparation interfaces, our products are compatible with each other. Leave BLAST in the vehicle and put SPART on your back to protect your squad on the move. Yes, SPART packs incomparable power and outstanding detection and jamming capability into a format so compact and lightweight that soldiers can carry it on their backs or in their hands without difficulty.



SPART uses AI to protect forces
SPART, like all reactive jammers in the MC2 Technologies range, such as BLAST and MAJES DFB6, is compatible with the ILIAD* module. Based on AI, it offers enhanced capabilities in terms of detection, identification and neutralization of uncommon threats. In addition to its ability to scramble multiple threats simultaneously, it can identify the type of drone and/or communication protocol used, and discriminate between enemy and friendly drones. In this way, it determines the precise parameters for effective jamming without affecting other types of communication.
ILIAD* (Interface de Lutte Intelligente Anti Drone) is the module developed as part of the OASIS (On-board Smart jamming System) program run by DGA-MI and AID with support from AMIAD.